What is yourhope@airmail.cc ransomware?
There were a lot of older versions of Scarab ransomware, and yourhope@airmail.cc ransomware is the newest. There are no significant differences between them, still the virus is very infectious and dangerous for any system. yourhope@airmail.cc ransomware can block all the personal files on your computer and makes it unreadable. First yourhope@airmail.cc infiltrates your system, then starts encrypting procedure with AES encryption algorithm. This ransomware adds .yourhope@airmail.cc file extension to the name of all the encrypted data. In this article you can learn how to remove yourhope@airmail.cc ransomware and decrypt .yourhope@airmail.cc files.
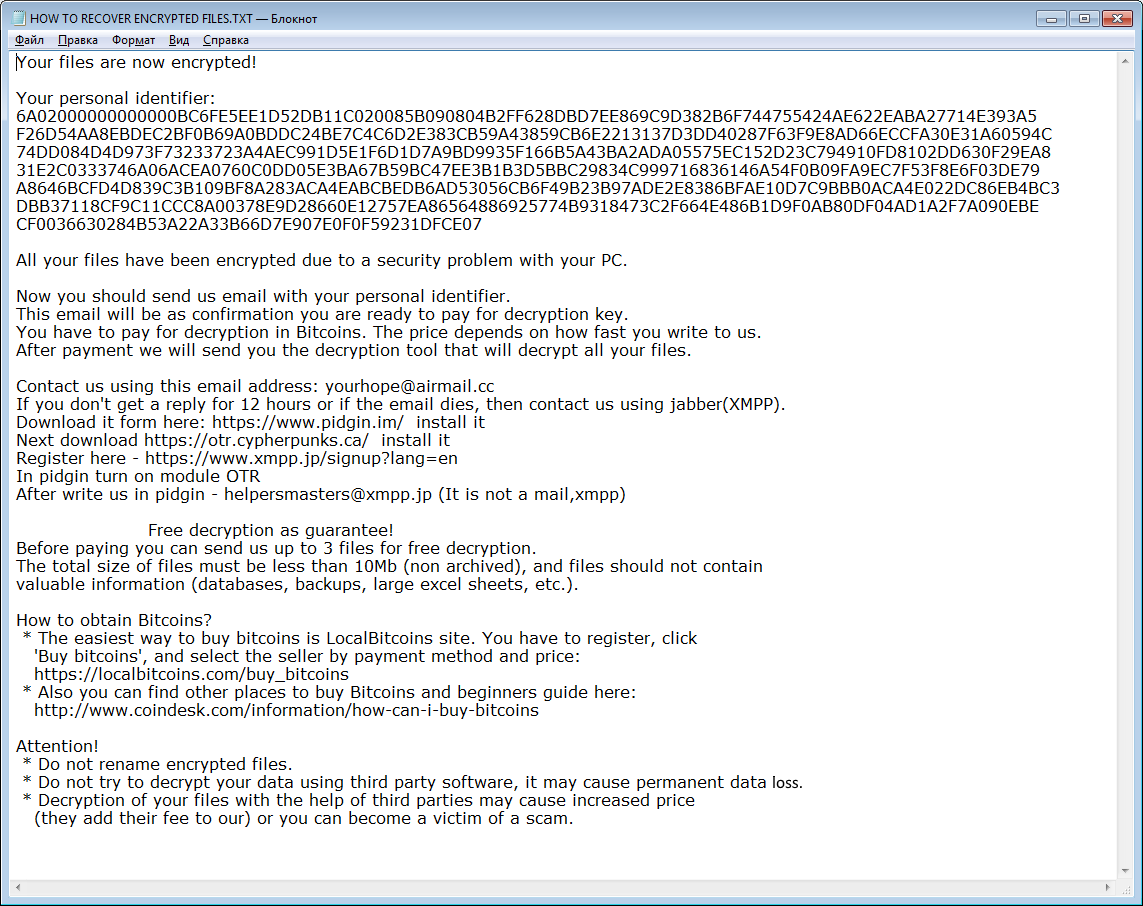
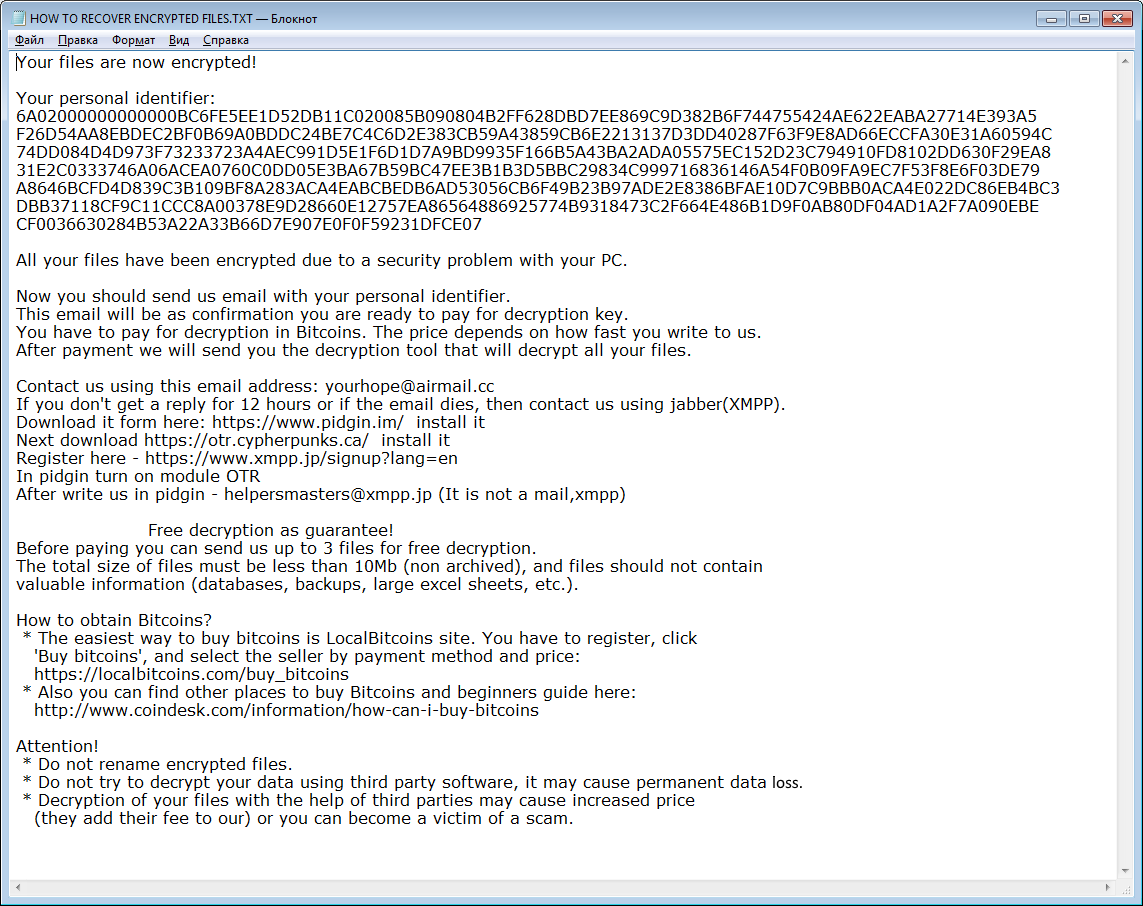
Once data on your computer is encrypted, yourhope@airmail.cc will drop HOW TO RECOVER ENCRYPTED FILES.TXT file. You can find demands and instruction on how to pay the ransom for decryption key in this text file. This is what yourhope@airmail.cc ransom note contains:
Your files are now encrypted!
Your personal identifier:
6A02000000000000***1DFCE07
All your files have been encrypted due to a security problem with your PC.
Now you should send us email with your personal identifier.
This email will be as confirmation you are ready to pay for decryption key.
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.
Contact us using this email address: yourhope@airmail.cc
If you don’t get a reply for 12 hours or if the email dies, then contact us using jabber(XMPP).
Download it form here: https://www.pidgin.im/ install it
Next download https://otr.cypherpunks.ca/ install it
Register here – https://www.xmpp.jp/signup?lang=en
In pidgin turn on module OTR
After write us in pidgin – helpersmasters@xmpp.jp (It is not a mail,xmpp)
Free decryption as guarantee!
Before paying you can send us up to 3 files for free decryption.
The total size of files must be less than 10Mb (non archived), and files should not contain
valuable information (databases, backups, large excel sheets, etc.).
How to obtain Bitcoins?
* The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click
‘Buy bitcoins’, and select the seller by payment method and price:
https://localbitcoins.com/buy_bitcoins
* Also you can find other places to buy Bitcoins and beginners guide here:
http://www.coindesk.com/information/how-can-i-buy-bitcoins
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software, it may cause permanent data loss.
* Decryption of your files with the help of third parties may cause increased price
(they add their fee to our) or you can become a victim of a scam.
yourhope@airmail.cc is a typical ransomware, its main purpose is to force you to pay them. After finishing encrypting process, the ransomware will state that there are no ways to recover your files but to pay ransom. Cyber criminals demand ransom in BitCoins. Once you’ve done payment, they are suppose to send you decryption key. But you should know that cyber criminals are not going to give you a decryption key. Mostly they are just ignoring their victims. That’s why there is no need to contact them, it wouldn’t help. Still, yourhope@airmail.cc ransomware does very complicated encryption, but it does not damage, move or delete your files, which means you have chance to restore your personal data.
How to remove yourhope@airmail.cc from your computer?
Unfortunately, there are no possible ways to remove yourhope@airmail.cc ransomware manually, because the infection goes too deep into your system. You may remove the virus only with automatic removal tool, try this one to clean your system from yourhope@airmail.cc ransomware.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt files encrypted by yourhope@airmail.cc?
Once you’ve removed virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Decrypt files with automated decryption tools
Unfortunately, due to novelty of yourhope@airmail.cc ransomware, there are no available automatic decryptors for this virus yet. Still, there is no need to invest in malicious scheme by paying ransom. You are able to recover files manually.
Decrypt files manually
You can try to use one of these methods in order to restore your encrypted data manually.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
How to protect PC from yourhope@airmail.cc?

It’s pretty difficult task to get rid of any ransomware, including yourhope@airmail.cc. But you can easily prevent any infection of your PC. HitmanPro.Alert’s CryptoGuard can help you with this problem. It’s one of the best anti-ransomware applications. No matter how sneaky it is, HitmanPro.Alert’s CryptoGuard will stop yourhope@airmail.cc infiltration to your system. After detection, this program removes all the related to the ransomware data and prevents your file from being encrypted.