What is Zero-Fucks Ransomware?
In this article, we will look at how to remove Zero-Fucks Ransomware and decrypt .zerofucks files. Zero-Fucks Ransomware is a new threat, namely a cryptovirus penetrating a PC through unprotected user networks. Zero-Fucks Ransomware encrypts user data and makes these files unusable and unreadable. This changes the extension of these files to .zerofucks, then creates a text file Bitcoin_Address.txt that specifies the conditions for the purchase of the decryption key. Also, a popup blocking window can act as a scam note.
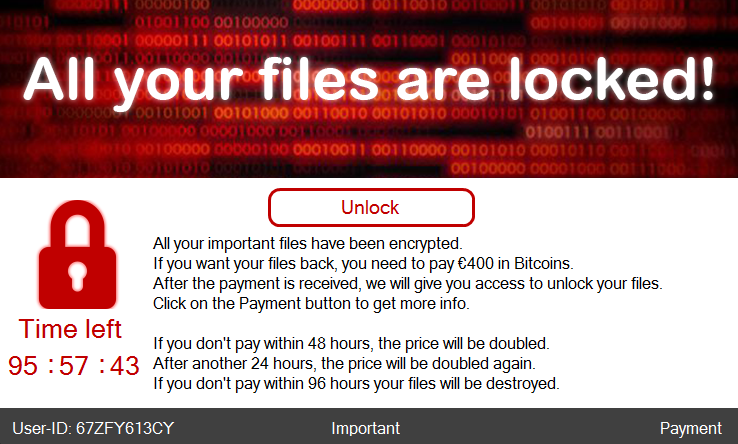
The note scammers use various methods of intimidation. For example, it says that after 48 hours the repurchase price will increase from 400 to 800 euros. After 72 hours, the price will be 1,600 euros, and after 96 hours the files will be permanently deleted if the ransom is not paid.
It is also worth noting that the virus removes shadow copies of files and system restore points. This is done in order to complicate file recovery. The ransom must be paid in bitcoin equivalent. Cryptocurrency is not chosen by chance, because this is how attackers manage to hide their activity. We do not recommend you pay intruders. The best way is to learn our guides to remove Zero-Fucks Ransomware and decrypt .zerofucks files.
Update: Use following service to identify the version and type of ransomware you were attacked by: ID Ransomware. If you want to decrypt your files, please follow our instruction below or, if you have any difficulties, please contact us: submit@securitystronghold.com. We really can help to decrypt your files.
How to remove Zero-Fucks from your computer?
You may try to use anti-malware tool to remove Zero-Fucks ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .Zero-Fucks files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Zero-Fucks ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows Zero-Fuckss copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D

