What is PZDC Ransomware?
PZDC is a cryptovirus that encrypts data on servers and requires a ransom of 100 Monero. The virus encrypts database data files using GnuPG. The PZDC acquired particular distribution in the middle of June of this year, and it was originally aimed at two categories of users, namely English-speaking and Russian-speaking. However, cryptovirus has spread everywhere, in all corners of the world. That is why the question of how to delete PZDC Ransomware and decrypt .pzdc files is very acute. Below we have placed the image and the content of the attacker’s note 1_VIRUS_SHIFROVALSHIK.txt, which contains their requirements:
English part:
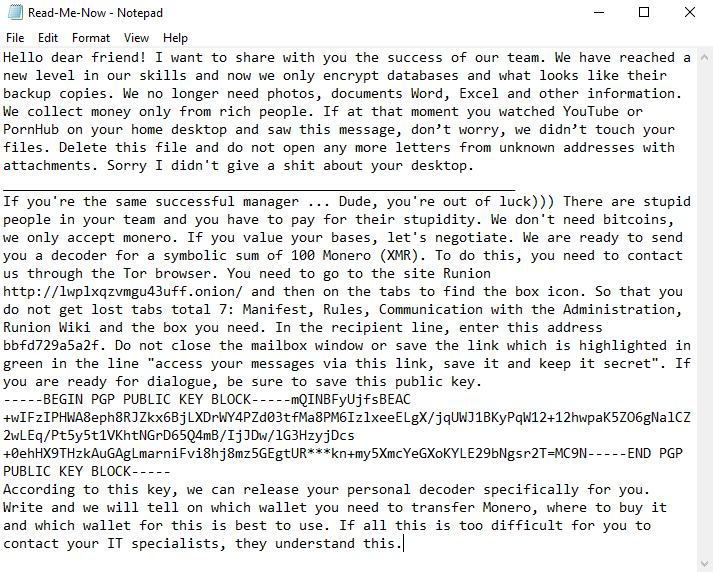
Hello dear friend! I want to share with you the success of our team. We have reached a new level in our skills and now we only encrypt databases and what looks like their backup copies. We no longer need photos, documents Word, Excel and other information. We collect money only from rich people. If at that moment you watched YouTube or PornHub on your home desktop and saw this message, don’t worry, we didn’t touch your files. Delete this file and do not open any more letters from unknown addresses with attachments. Sorry I didn’t give a shit about your desktop.
________________________________________________________________
If you’re the same successful manager … Dude, you’re out of luck))) There are stupid people in your team and you have to pay for their stupidity. We don’t need bitcoins, we only accept monero. If you value your bases, let’s negotiate. We are ready to send you a decoder for a symbolic sum of 100 Monero (XMR). To do this, you need to contact us through the Tor browser. You need to go to the site Runion http://lwplxqzvmgu43uff.onion/ and then on the tabs to find the box icon. So that you do not get lost tabs total 7: Manifest, Rules, Communication with the Administration, Runion Wiki and the box you need. In the recipient line, enter this address bbfd729a5a2f. Do not close the mailbox window or save the link which is highlighted in green in the line “access your messages via this link, save it and keep it secret”. If you are ready for dialogue, be sure to save this public key.
—–BEGIN PGP PUBLIC KEY BLOCK—–mQINBFyUjfsBEAC+wIFzIPHWA8eph8RJZkx6BjLXDrWY4PZd03tfMa8PM6IzlxeeELgX/jqUWJ1BKyPqW12+12hwpaK5ZO6gNalCZ2wLEq/Pt5y5t1VKhtNGrD65Q4mB/IjJDw/lG3HzyjDcs+0ehHX9THzkAuGAgLmarniFvi8hj8mz5GEgtUR***kn+my5XmcYeGXoKYLE29bNgsr2T=MC9N—–END PGP PUBLIC KEY BLOCK—–
According to this key, we can release your personal decoder specifically for you. Write and we will tell on which wallet you need to transfer Monero, where to buy it and which wallet for this is best to use. If all this is too difficult for you to contact your IT specialists, they understand this.
The note is written in two languages and contains the address of the site through which users need to contact the scammers and pay the ransom. The amount of repurchase is equal to the cost of a good car because at the moment 100 XMR is equal to 11,139 USD. This is big money! Do not pay intruders, there is no guarantee that your files will really be decrypted as it should. Below you will find our recommendations and instructions that will help you to remove PZDC Ransomware and decrypt .pzdc files.
Update: Use following service to identify the version and type of ransomware you were attacked by: ID Ransomware. If you want to decrypt your files, please follow our instruction below or, if you have any difficulties, please contact us: submit@securitystronghold.com. We really can help to decrypt your files.
How to remove PZDC from your computer?
You may try to use anti-malware tool to remove PZDC ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .PZDC files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of PZDC ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D