What is Litar Ransomware?
Litar is a cryptovirus that is part of the STOP (DJVU) Ransomware family. You need to remove Litar Ransomware and decrypt .litar files, and that’s why. Like other crypto viruses of this family, Litar penetrates the victim’s computer and encrypts user data of various formats, which are usually very significant for the user. For example, it encrypts audio files, video, multimedia, archives or office documents and much more. Of course, no user wants to lose their important data, and that’s what attackers use. As soon as Litar penetrates the PC, it changes the file extensions to .litar, which contributes to the complete unreadability of the files. Also, after the above, the virus throws a special note file _readme.txt with information about the methods of redemption and the requirements of intruders. These files are located in each folder with infected files. This is what this note looks like:
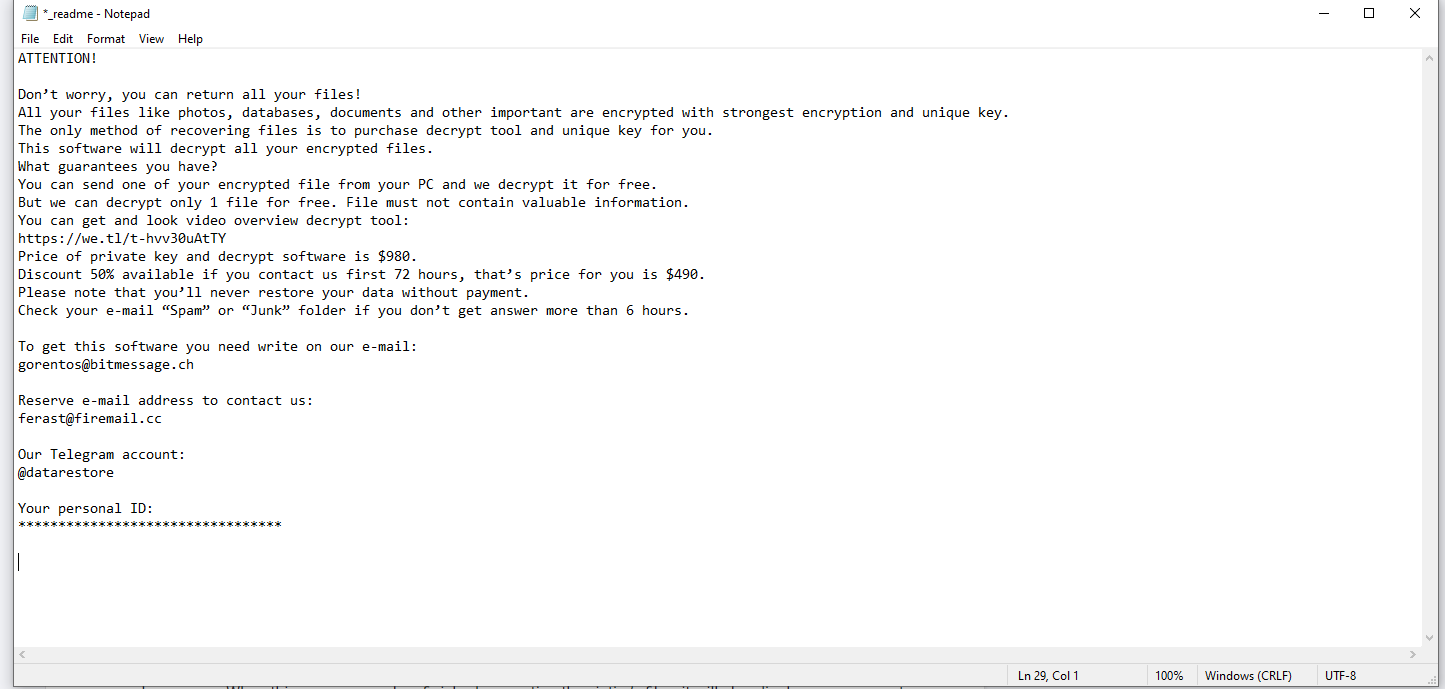
Here is the text from the note:
Hello.
All your files have been encrypted due to a security problem with your PC.
For information on decoding, please write to the e-mail AliMussafenLibat@protonmail.com
Your files are now encrypted!
Your personal identifier:
+4IAAAAAAAC***ZNRlDk
Now you should send us email with your personal identifier.
Contact us using this email address: AliMussafenLibat@protonmail.com
Free decryption as guarantee!
Before paying you can send us up to 3 files for free decryption.
The total size of files must be less than 5Mb (non archived), and files should not contain
valuable information (databases, backups, large excel sheets, etc.).
Attention!
* Do not rename encrypted files.
* Do not try to decrypt your data using third party software, it may cause permanent data loss.
* Decryption of your files with the help of third parties may cause increased price
(they add their fee to our) or you can become a victim of a scam.
GeorjeHalique@protonmail.com
Litar is in many ways similar to similar threats from STOP Ransomware family. Fraudsters offer the user to pay a ransom in the first 72 hours to get a 50% discount. With the discount, the redemption amount is $ 490. It should be noted that the ransom must be paid in cryptocurrency, for example in bitcoins. This is intended to avoid harassment by law enforcement officers.
And so, we do not recommend you to pay fraudsters because no one and nothing can guarantee you that your files will be truly decrypted. See our recommendations and instructions to remove Litar from your PC and decrypt all the files.
How Litar Ransomware gets into PC?
Attackers are very sophisticated. For example, Litar may come along with free downloads from web. Penetration of such programs is invisible to the user. In some cases, crypto viruses, such as Litar, come to the PC in the form of some programs, or rather portable versions of these programs. Also, Litar can come as an attachment to a spam mailing list or as an update for a program or utility. This happens because many users do not use paid versions of antiviruses, and in some cases, do not use similar programs at all. Remember that preventing the entry and attack of a cryptovirus is easier than dealing with the consequences of its activity. If it so happens that your files are encrypted, then use our recommendations and remove Litar and decrypt .litar files.
Update: Use following service to identify the version and type of ransomware you were attacked by: ID Ransomware. If you want to decrypt your files, please follow our instruction below or, if you have any difficulties, please contact us: submit@securitystronghold.com. We really can help to decrypt your files.
How to remove Litar from your computer?
You may try to use anti-malware tool to remove Litar ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .Litar files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Litar ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D
