Article’s Guide
- What does [*id*][encrypter@cock.li].ccc stand for?
- CCC ransomware encryption process.
- How to remove CCC Ransomware from your computer
- How to decrypt [*id*][encrypter@cock.li].ccc files
- Data Recovery
- Automated decryption tools
- Other software
What does [*id*][encrypter@cock.li].ccc stand for?
Recently internet users faced the new threat, that we can call CCC ransomware. This virus doesn’t belong to any already known file-encryption ransomware family. However, it has a lot in common with LockBit ransomware, with the viruses of STOP(DJVU) ransomware family:HETS, HETS, MSOP, ZOBM, ROTE, MBED, PEET, GROD, MOSK, TOEC, NAKW, Derp, COOT, Nols, Werd, Ndarod, Leto, Bora and RECO; and DHARMA ransomware viruses: KHARMA, newer version of MONEY, Money, Oo7 and CASH. CCC ransomware can potentially infect every computer, as the hackers use various tricks to spread it. For example, they can easily infect a computer through the remote access port and no one won’t even notice it. Moreover, creators of such viruses also create fake installators and spread them by the means of fake websites, that disguise themselves as the real ones. If CCC ransomware successfully gets in the system, it immediately begins the encryption process. We should warn you, don’t try to decrypt [*id*][encrypter@cock.li].ccc files by the means of the file renaming or other changings. It can damage your files permanently without any hope to restore them.
CCC ransomware encryption process.
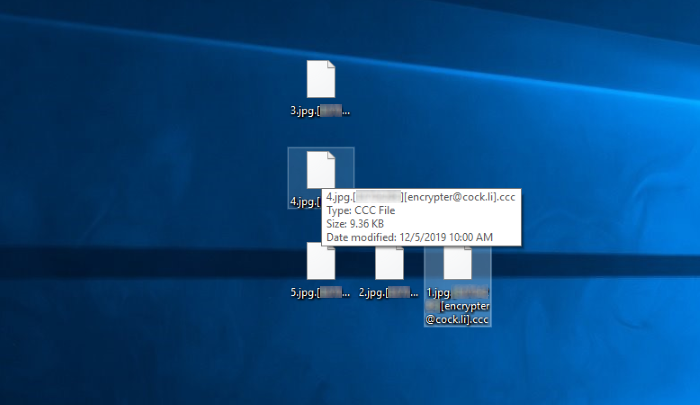
CCC ransomware encryption is the two-step process, the process of which occurs in the strict order. At first the virus is to find appropriate files to encrypt. These files may vary from media files and documents to executable and dynamic link libraries ones. However, nowadays it attacks only documents and media files. This formats are chosen not by chance: in the most cases these files are the most valuable information on a computer and it’s impossible to restore them manually. As soon as the appropriate files are found, CCC ransomware begins to modify their structures and makes them unreadable by any program. As the result, the files get new extension – [*id*][encrypter@cock.li].ccc. The id is a unique for every user and is used by the hackers to decrypt the files, according to their words. This information can be found in the ransom note, that is called ReadMe.txt. However, we strongly advice you to avoid any contact with them. There is a great risk, that everything can become much worse. They can easily ignore you, make you pay twice or infect your computer with the more malicious malware, like RAT. You’d better try our solution, if you really need to remove CCC ransomware and decrypt [*id*][encrypter@cock.li].ccc files!
_____________________ccc Ransomware_______________________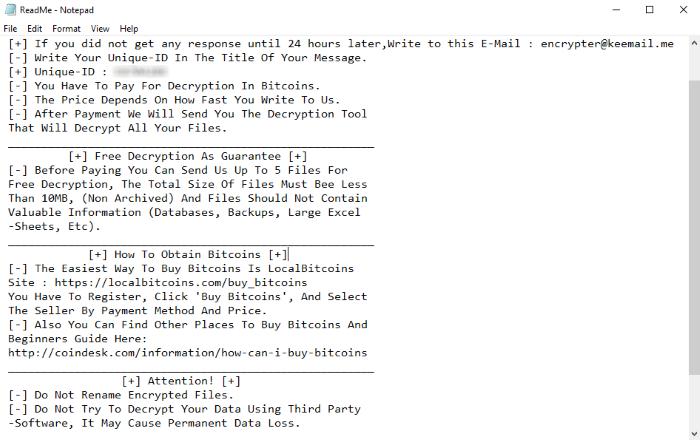
ReadMe.txt
[+] Write Us To The E-Mail : encrypter@cock.li
[+] If you did not get any response until 24 hours later,Write to this E-Mail : encrypter@keemail.me
[-] Write Your Unique-ID In The Title Of Your Message.
[+] Unique-ID : *ID*
[-] You Have To Pay For Decryption In Bitcoins.
[-] The Price Depends On How Fast You Write To Us.
[-] After Payment We Will Send You The Decryption Tool
That Will Decrypt All Your Files.
_______________________________________________________
[+] Free Decryption As Guarantee [+]
[-] Before Paying You Can Send Us Up To 5 Files For
Free Decryption, The Total Size Of Files Must Bee Less
Than 10MB, (Non Archived) And Files Should Not Contain
Valuable Information (Databases, Backups, Large Excel
-Sheets, Etc).
_______________________________________________________
[+] How To Obtain Bitcoins [+]
[-] The Easiest Way To Buy Bitcoins Is LocalBitcoins
Site : https://localbitcoins.com/buy_bitcoins
You Have To Register, Click 'Buy Bitcoins', And Select
The Seller By Payment Method And Price.
[-] Also You Can Find Other Places To Buy Bitcoins And
Beginners Guide Here:
http://coindesk.com/information/how-can-i-buy-bitcoins
_______________________________________________________
[+] Attention! [+]
[-] Do Not Rename Encrypted Files.
[-] Do Not Try To Decrypt Your Data Using Third Party
-Software, It May Cause Permanent Data Loss.
[-] Decryption Of Your Files With The Help Of Third
Parties May Cause Increased Price (They Add Their Fee
To Our) Or You Can Become A Victim Of A Scam.
How to remove CCC Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove CCC from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like CCC, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt [*id*][encrypter@cock.li].ccc files?
Once you’ve removed the virus, you are probably thinking how to decrypt .[*id*][encrypter@cock.li].ccc files or at least restore them. Let’s take a look at possible ways of decrypting your data.
Restore [*id*][encrypter@cock.li].ccc files with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Decrypt [*id*][encrypter@cock.li].ccc files with other software
Unfortunately, due to the novelty of CCC ransomware, there are no decryptors that can surely decrypt encrypted files. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Decrypt .ccc files with Emsisoft decryptor
This software includes information about more than 100 viruses of STOP(DJVU) family. All that you need are two files or some luck. You can freely use it as it distrubetes free of charge. If it doesn’t work for you, you can use another method.
Restore .ccc files with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .ccc files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
This software includes information about more than 100 viruses of STOP(DJVU) family. All that you need are two files or some luck. You can freely use it as it distrubetes free of charge. If it doesn’t work for you, you can use another method.
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .ccc files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.