What is Acuf2 Ransomware?
Acuf2 ransomware is one of the most wide-spread file encryptors and belongs to the Dharma ransomware family. Such malicious programs as Acuf2 ransomware have a common feature – they encrypts files and add an appendix in the end of the file. In the case of Acuf2 ransomware infection this appendix is .Acuf2. Many users try to remove Acuf2 ransomware infection by changing the name of the file, but it’s useless (encryptors change the structure of the program) The reason of making such malicious programs is quite clear – intruders want to make you pay them. They also often leave a .txt file with their proposal. Such text messages are characterized by using some psychological techniques, such as they can try to make you fell comfortable or they also try to make you think, that their proposal is a good deal. If we are talking about Acuf2 message, the file is RETURN FILES.txt, let’s look into it:
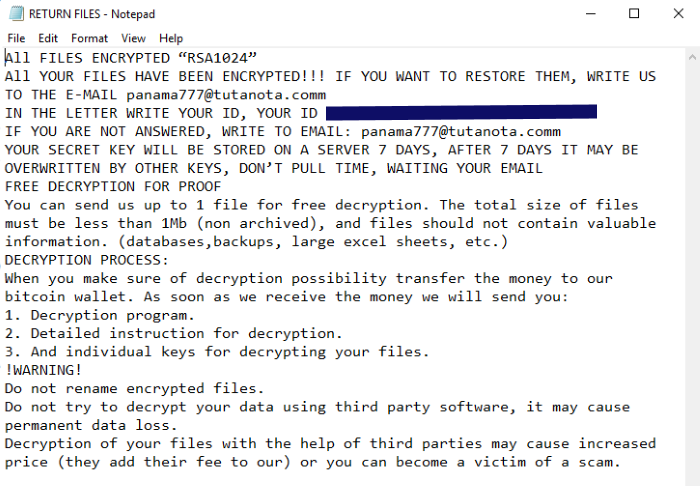
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL panama777@tutanota.comm
IN THE LETTER WRITE YOUR ID, YOUR ID *number*
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: panama777@tutanota.comm
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Here you can see that hacker wants to make you pay him as soon as possible, otherwise your files will be encrypted forever. Don’t pay him a cent! There is no guarantee that he will honor his promise. If you want to decrypt your files, you may follow our guide on how to remove Acuf2 ransomware and decrypt .Acuf2 files.
Article’s Guide
- How to remove Acuf2 Ransomware from your computer
- How to remove Acuf2 Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove Acuf2 Ransomware from your computer?
You may try to use SpyHunter anti-malware tool to remove Acuf2 Ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to remove Acuf2 Ransomware encryption from your files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Madek ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows Todars copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.

