What does “ransomware” mean?
Nowadays, the internet is full of various threats. The one of them is ransomware viruses. In this article we would like to tell you about the ways hot to prevent ransomware attacks and describe the mechanism they use. Generally, they belong to already known family of viruses, such as STOP(DJVU) or Dharma. However, sometimes hackers create unique ransomwares whose encryption algorithms are unique too. In the most cases, ransomware viruses sneak into the system by the means of fake installers. They can be easily found nearly everywhere on the internet. Hackers even create fake websites to promote such installers. In this case, both installer and site, imitate the original ones. Sometimes hackers use Remote Access Terminals, such as ScreenConnect. The main source of such programs is various bundles, the terms of installation of which are not always clear. Moreover, hackers can send you a malicious email. They inject the code of the virus into a regular and harmless file and then send it by email. The function of the messages is to lure victims to open the file. In this case, the operating system will execute the code of a various together with the opening of the file. That’s why it’s important to have a firewall and a strong antivirus protection. Such software can help you to prevent a possible ransomware attack beforehand.
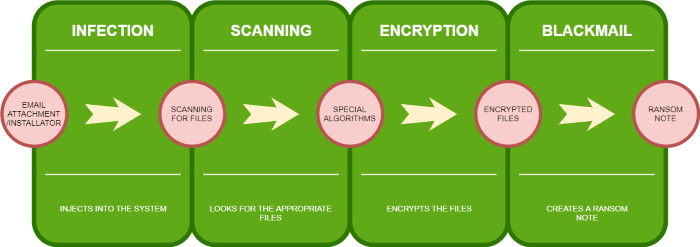
When ransomware virus is in the operating system, it changes the registry keys and modifies their values. Then it infects the legitable system processes by the means of which it encrypts the files. Some of the ransomwares also establishes connection with various IP addresses for various reasons. For example, hackers use it in order to set the unique encryption key. When the encryption process is done, the files get new extensions, which are unique for every virus. Some of them also contain ID numbers or contact emails. Then the virus usually drops the ransom note. They can be of various formats. Some of the viruses create simple “.txt” files, some of them shows pop-up messages, some of them even create an application, that can be used to decrypt the files. The main purpose of such notes is to make victims to purchase a decryption tool, but in the most cases, hackers don’t respond to the messages after being paid. However, the surest way to decrypt your data is to buy the decryption tool, but we strongly recommend you not to do it. For this reason, we prepare the guide on how to remove ransomwares and decrypt your files for every unique case. Now let’s talk about how to prevent ransomware attacks.
How to create a backup?
Backup – is a copy of data taken and stored elsewhere so that it may be used to restore the original files after a data loss event. This way takes the first place as the most effective one. The best steps you can take to protect your data is to make backups of your data. We recommend you to keep backups on separate computers or external removable disks and cloud services. In case of physical drives, they should be restricted from any internet or local connections. Ransomware viruses sometimes attack not only a single computer, but they infect local networks as well. Regarding to this fact, you’d better make as many backups on physical devices as possible. Moreover, you should use only high-quality products. It will diminish the chances of losing the data because of the corrupted hard drive to minimal levels. Furthermore, the software you use to make the backups should also prove the quality. For this reason we recommend you to use Stellar Data Recovery. This soft can easily make backups of your data on the physical drives and moreover, it can restore your files both from shadow copies and created backups! This software has proven to be very appreciated by customers, who have faced ransomware problems!

The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-$299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to create a cloud backup?
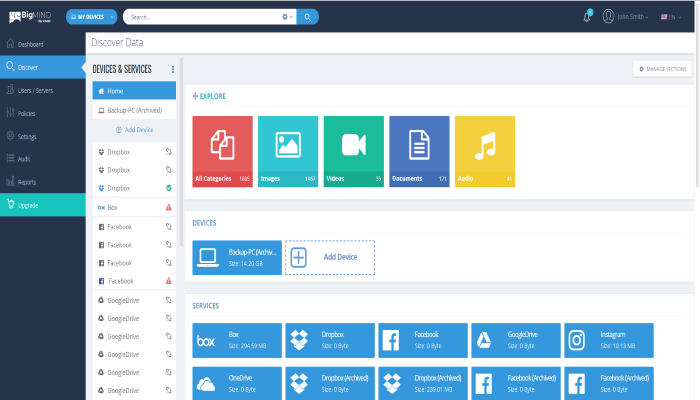
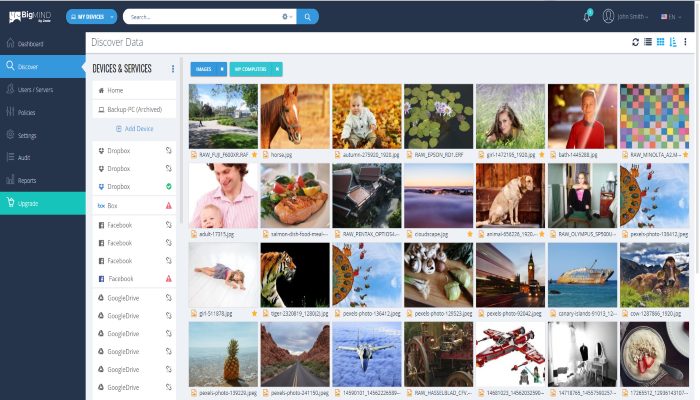
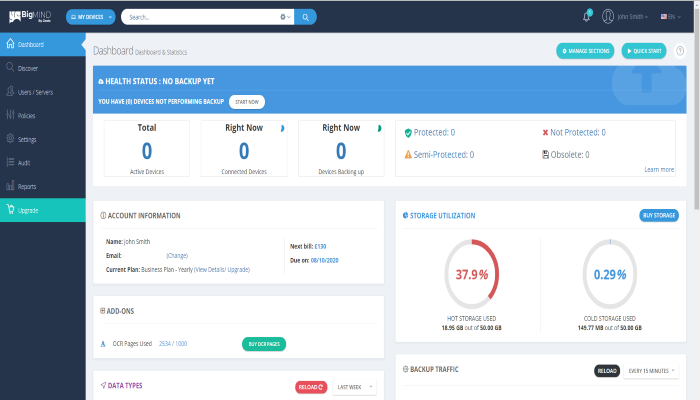
Everything is very simple here. If you really want to protect from ransomware attacks you should use cloud backup services. Such services give you an opportunity to not worry about the safety of your backups and provide you with immediate access to your data. The best choice here is BigMIND. This service has a user friendly interface and it becomes very easy to keep your data safe from ransomware attack! You don’t need any technical skill or even an IT degree to use it. Just upload your data on the site and the unique A.I. technology will do the rest. Moreover, you can connect several devices with BigMIND and you will get the access to all your data! Furthermore, this service has a lot of other features, try them now!

How to use a firewall?
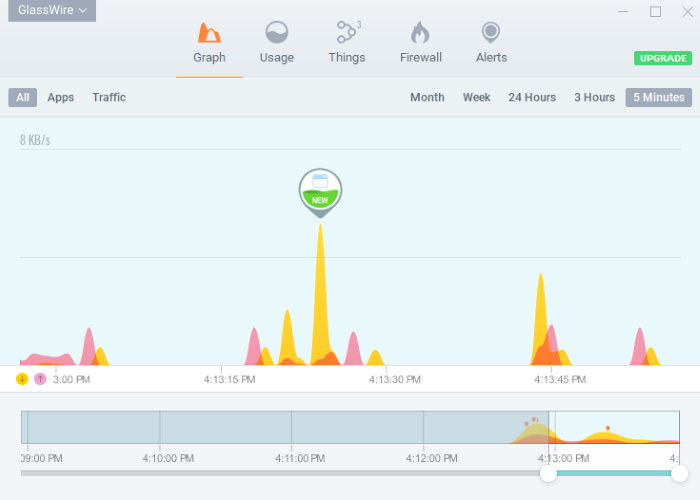
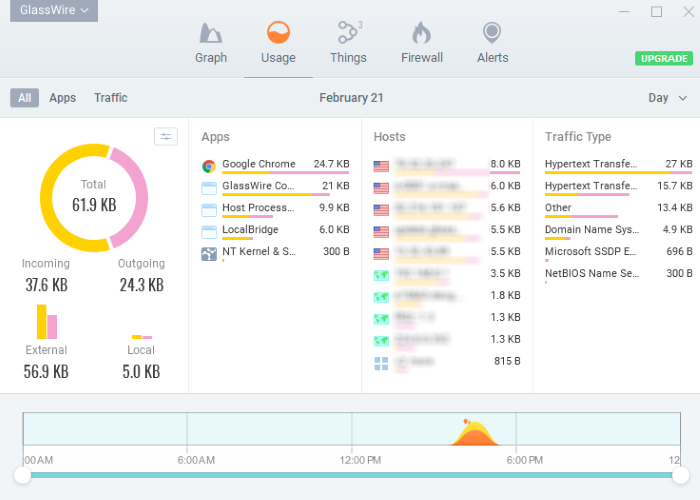
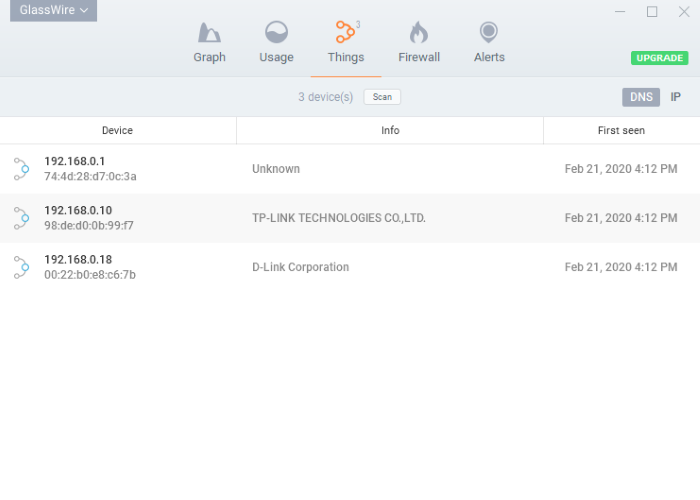
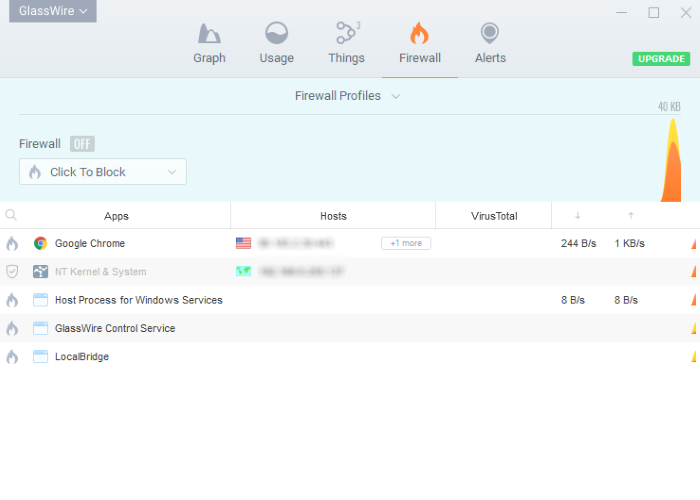
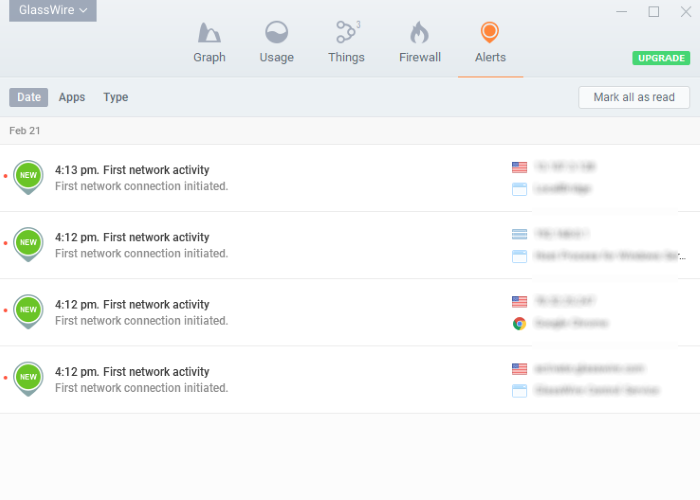
The use of firewall takes the second place. A firewall is a protective software for networks, both corporate and individual. It filters the incoming and outgoing traffic, which can be potentially dangerous. A high-quality firewall can easily show you the source of the traffic, warn you, if a new connection was established and gives you an opportunity to block the traffic sources. We consider that the GlassWire is the best product nowadays. This user-friendly software has proven its quality through the years. With the help of GlassWire it’s easy to prevent any ransomware or hacker attack.
To unlock all features and tools, purchase is required ($49.99-$299). By clicking the button you agree to EULA and Privacy Policy.
Nowadays, it’s all suitable solutions. However, we’ve not mentioned RDP closing solution yet, but we will do it a bit later. For now we recommend you to undertake all above mentioned solutions, as they are the most effective ones at the present moment.