What is Vortex?
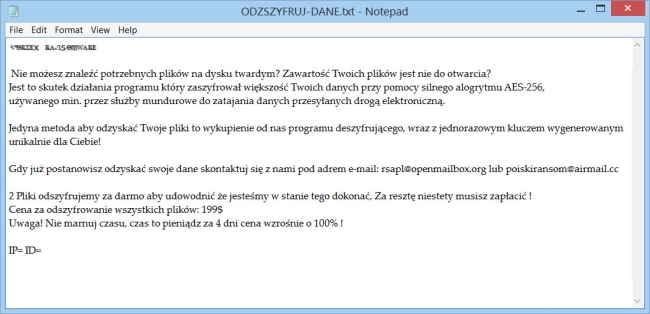
Vortex is a ransomware-type virus developed by Polish hackers. This virus uses AES-256 cryptography to encode user’s personal files including photos, documents, videos and so on. During the encryption, all affected files are appended with .aes (or .ZABLOKOWANE) extension. For example, myfamily.jpg is changed to myfamily.jpg.aes. After this, it creates TXT file (ODZSZYFRUJ-DANE.txt or #$# JAK-ODZYSKAC-PLIIKI.txt), placing it on the desktop. Vortex ransomware spreads by means of spam emails disguised as invoices for any service, messages from bank, discount coupons in the store and so on. Basically, all that can generate curiosity. That’s why you should be careful when receiving emails from unknown addresses. Always check for viruses email attachment before opening it!!!
Here is used a typical scheme of all ransomware-type viruses – to make victims pay them. The only differences between them are the ransom price ($199) and encryption method. Cyber criminals state that there are no ways to recover your files but to pay a ransom. Once payment is done, they are supposed to send you decryption key. But you should know that nobody can guarantee that they will fulfill their end of the bargain. The practice shows that cyber-criminals just ignore people who paid them. That’s why you should not be pushed about by them because you can remain without money and files. On the contrary, you only may encourage them to continue their dirty business. In any case, you will be simply scammed. You need to decrypt your files, but you should know that it is impossible without removing the virus from your computer. Unfortunately, to date, there are no decryption tools available for the Vortex ransomware. As soon as it appears, we’ll be sure and let you know. But for now, you can try to use manual methods which imply the use of features of the operating system to decrypt your files.
How to remove Vortex from your computer?
The best and easiest way to remove Vortex from your computer is to use special anti-malware program that has this threat in its database. As stated above, you need proper and reliable anti-malware program, that’s why we recommend you to use SpyHunter.
It scans your computer and detects various threats like Vortex, then completely removes it. One of the best features of this program – large threat’s database. SpyHunter’s newly advanced ransomware detection technology is able to run an instant ransomware scan and show you a message about detection. After deep scanning of your system, it will easily find and delete Vortex. Use this removal tool to get rid of Vortex ransomware for FREE.
How to decrypt .aes files encrypted by Vortex?
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Decrypt .aes files manually
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.