What is .ciphered?
Recently, the new internet threat has been found. It’s called TurkStatik ransomware. This virus doesn’t belong to any already known virus family and can be described as the file-encryption ransomware. It’s a unique virus, but at the same time it has a lot in common with such families, as STOP(DJVU) ransomware family:ZOBM, ROTE, MBED, PEET, GROD, MOSK, TOEC, NAKW, Derp, COOT, Nols, Werd, Ndarod, Leto, Bora and RECO; and DHARMA file-encryption ransomware family the members of which are: KHARMA, newer version of MONEY, Money, Oo7 and CASH. These viruses infect computers by the means of backdoors in the operating system and software. Hackers inject the code of the virus into a harmless file and then spread it by the means of email attachments, torrents and free file sharing services. These files can hardly be differed from the harmless ones and it’s easy to become infected with it. If your system has been accidentaly infected with TurkStatik ransomware, don’t try to decrypt .ciphered files manually! Every changing of the encrypted file can corrupt it permanently!
TurkStatik ransomware encryption process.
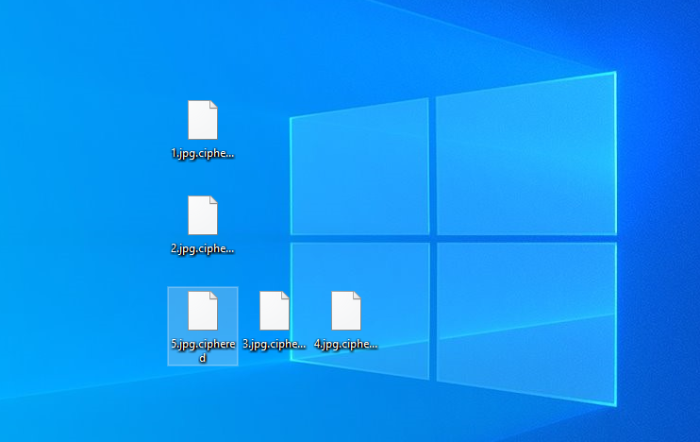
Once TurkStatik gets into the system, it immediately begins the encryption process, that can be described as the two-step one. At first, the virus needs to find files suitable for encryption. This virus can modify only definite file formats and among them are all formats of documents and a great variety of media files. Once the files have been founded it begins to modify their structures and makes them unreadable. As the result, the files have new .ciphered extension. Then it creates the ransom note, that is called README_DONT_DELETE.txt. The message is written in Turkish and aims at definite country, but it can possibly infect everyone. The message aims at forcing the user to pay the ransom for decryption services, that hackers offer. We strongly recommend you to avoid all contacts with them. they can easily make the situation much worse. That’s why we’ve prepared the detailed guide to help you.
README_DONT_DELETE.txt
Bu yöntemler sadece sizin zaman kaybetmenize sebep olacaktir.
Yinede veri kurtarma firmalari yada programlari kullanmak isterseniz lütfen asil dosyalariniz üzerinde degil,
bunlarin kopyalari üzerinde islem yapiniz ve/veya yaptiriniz.
Asil dosyalarin bozulmasi verilerinizin geri dönülemez sekilde zarar görmesine sebep olabilir.
Sifrelenen dosyalarinizin asillari, üzerine rast gele veri yazma teknigi kullanilarak silinmistir.
48 saat içerisinde dönüs yapilmadigi taktirde, sistemede kullanilan sifre silinecektir ve verileriniz asla geri döndürülemeyecektir.
Diskleriniz Full disk encryption ile sifrelenmistir yetkisiz müdahale kalici veri kaybina neden olur!
Para Verseniz Daha Açmazlar Diyen Bilgisayarcilara veya Parani Alir Dosyalarini Vermez Diyen
Etrafinizdaki insanlara inanmayin
Size Güven Verecek Yeterli Referansa Sahibim
Sizi tanimiyorum, dolayisi ile size karsi kötü duygular beslememin size kötülük yapmamin bir anlami da yok,
amacim sadece bu isten bir gelir elde etmek. Yaptiginiz ödeme sonrasinda
en kisa zamanda verilerinizi eski haline getirmek için sunucunuza baglanacagim.
24 saat içerisinde dönüs yapilmadigi taktirde, sistemede kullanilan sifre silinecektir ve verileriniz asla geri döndürülemeyecektir.
Verilerinizin sifresini çözdürmek için asagidaki iletisim kanalindan bizlere ulasabilirsiniz.
Ulasmak istediginide mutlaka asagida size özel üretilen kodu eklemeyi unutmayiniz.
SITE_CODE:
e-mail : decservice@mail.ru
recoverydbservice@protonmail.com
Article’s Guide
- How to remove TurkStatik Ransomware from your computer
- How to remove TurkStatik Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove TurkStatik Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove TurkStatik from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like TurkStatik, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt .ciphered files?
Once you’ve removed the virus, you are probably thinking how to decrypt .zobm files. Let’s take a look at possible ways of decrypting your data.
Restore .ciphered files with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Decrypt .ciphered files by other software
Unfortunately, due to the novelty of TurkStatik ransomware, there are no decryptors that can surely decrypt encrypted files. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Decrypt .ciphered files with Emsisoft decryptor
This software includes information about more than 100 viruses of STOP(DJVU) family. All that you need are two files or some luck. You can freely use it as it distrubetes free of charge. If it doesn’t work for you, you can use another method.
Restore .ciphered files with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .ciphered files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
This software includes information about more than 100 viruses of STOP(DJVU) family. All that you need are two files or some luck. You can freely use it as it distrubetes free of charge. If it doesn’t work for you, you can use another method.
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .ciphered files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.