What is Keypass?
Keypass is a new ransomware virus that encrypts personal files on the user’s PC and asks for ransom money. Although that virus is new, it works just like other ransomware. In order to penetrate the system, it uses deceptive emails, malicious exploits, pirated software, trojans, and various fake updaters. Following the successful penetration, the virus tries to bypass anti-malware systems and anything that may stop the virus. When it is done, it starts the encryption procedure. So, in order to be able to use encrypted files again, a victim is encouraged to transfer $300 to the cybercriminals’ account. We recommend you not to pay anything since nobody can guarantee that they will fulfill their end of the bargain. The practice shows that cybercriminals just ignore people after payment is done. In this article, you can learn how to remove Keypass ransomware and decrypt .KEYPASS files.
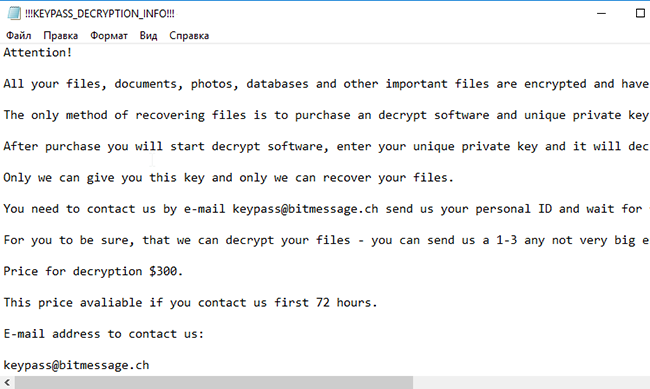
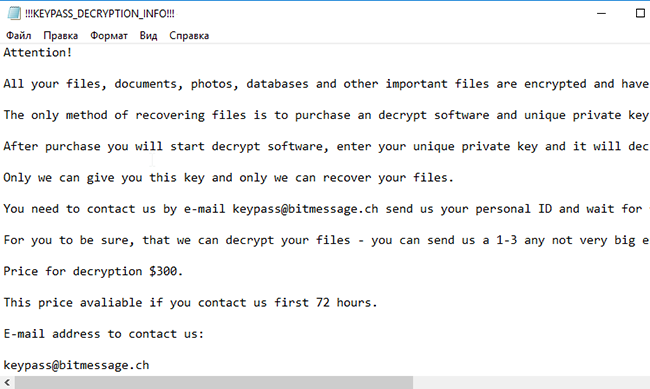
In order to encode victim’s data, Keypass Ransomware uses AES encryption algorithm. Under this method, the private ID key required for data recovery is created during the encryption process. After this, the user is no longer able to use affected files that have got .KEYPASS extension. For example, myfamily.jpg turns into myfamily.KEYPASS. Once encryption process is done, it creates !!!KEYPASS_DECRYPTION_INFO!!!.txt that contains the following text:
Attention!
All your files, documents, photos, databases and other important files are encrypted and have the extension: .KEYPASS
The only method of recovering files is to purchase an decrypt software and unique private key.
After purchase you will start decrypt software, enter your unique private key and it will decrypt all your data.
Only we can give you this key and only we can recover your files.
You need to contact us by e-mail keypass@bitmessage.ch send us your personal ID and wait for further instructions.
For you to be sure, that we can decrypt your files – you can send us a 1-3 any not very big encrypted files and we will send you back it in a original form FREE.
Price for decryption $300.
This price avaliable if you contact us first 72 hours.
E-mail address to contact us:
keypass@bitmessage.ch
Reserve e-mail address to contact us:
keypass@india.com
Your personal id:
3oea4X887i6AfaMLvQKS3QBoQIhKTsxmMaigPGfr
Still, Keypass ransomware does very sophisticated encryption, but it does not damage, move or delete your files, which means you have a chance to restore your personal data. For this, the first thing you got to do – to completely remove Keypass ransomware from your computer in order to exclude reinfection. You may take advantage of the benefits of an automated removal tool that will do it for you. Or you may use our manual guide, but keep in mind that this way is only recommended for experienced users.
How to remove Keypass from your computer?
You may try to use anti-malware tool to remove Keypass ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.

How to decrypt .KEYPASS files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Keypass ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.