What is Digisom?
Digisom is dreadful ransomware-type threat using asymmetric cryptography to infect your files. Once infiltrated, starts the scanning process to find the target files. Into the kill zone enters personal and sensitive files, like images, music, videos, text files and so on. Each file then gets “.3_random_characters.x” extension. For example, “photo.png” is renamed to “photo.pnggG3e.x”. After the encryption procedure, Digisom places ransom note in form 10 identical text files on the desktop (“Digisom Readme0.txt”, “Digisom Readme1.txt” up to “Digisom Readme9.txt”). You also might notice that your desktop wallpaper was changed to a solid black color.
Occasionally, a pop-up window will be appeared displaying timer until the next deletion of file. Merciless virus will delete one file every 2 hours. The ransom note contains instruction how to retrieve your files. Shortly said, cyber criminals demand an amount of .2 Bitcoin in exchange for your files. They also leave the link to a web site where the payment can be made anonymously. Once payment is confirmed, program connects to the server to verify it. If these conditions will be met, your data supposedly will be restored. However, you should not be pushed about by them because the victims who paid them are often ignored. In this case, you can remain without money and without files. From this article, you will learn how to remove Digisom Ransomare and some ways to decrypt .x files for FREE.
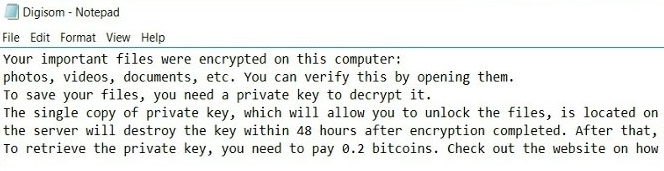
This is what text file Digisom Readme0.txt contains:
Your important files were encrypted on this computer: photos, videos, documents, etc. You can verify this by opening them.
To save your files, you need a private key to decrypt it.
The single copy of private key, which will allow you to unlock the files, is located on a secret server on the internet; the server will destroy the key within 48 hours after encryption completed. After that, nobody are able to restore the files.
To retrieve the private key, you need to pay 0.2 bitcoins. Check out the website on how to make payment: http://www.digisom.pw
YOUR UNIQUE ID TO FIND KEY:
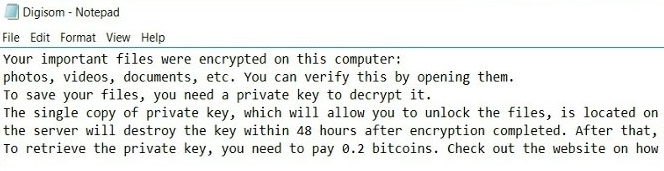
Here is what you can see on Digisom’s website:
1. Get Bitcoins (BTC) at localbitcoins.com if you don’t already have any.
2. Send 0.20004084 Bitcoins (in ONE payment) to the address below.
If you send any other bitcoin amount, payment system will ignore it !
Send EXACTLY 0.20004084 BTC (plus fees) to: 1FCuCww75NtxtVJHsvwaWJsphLsT1tRAoL
Bitcoins have not yet been received.
If you have already sent Bitcoins (the exact Bitcoin sum in one payment as shown in the box below), please wait a few minutes to receive them by Bitcoin Payment System. If you send any other sum, Payment System will ignore the transaction and you will need to send the correct sum again, or contact the site owner for assistance.
How Digisom infects your PC?
Like any other ransomware-type viruses, Digisom ransomware is distributed primarily through the fraudulent email messages. For example, it might be bill from tax company or online store like Amazon. The virus itself is hided within an attachment. Therefore, be very wary when opening files downloaded from suspicious emails or untrusted sources. Do not rush in these moments since you can compromise your system. The malware is also distributed through fake software updates, torrent (P2P) networks, and trojans as well.
To prevent suсh kinds of the threats as Digisom ransomware in the future follow these tips:
- Adjust your email anti-spam settings to filter out all potentially unsafe incoming messages.
- Make sure, the attachments with the following extensions: .js, .vbs, .docm, .hta, .exe, .cmd, .scr, and .bat. are in the black list
- Rename the vssadmin.exe process to protect Shadow Volume Copies of your files from removal.
- Raise the level of Firewall protection. It can prevent ransomware from connecting with its server.
- Do not forget to backup your files regularly. This will facilitate process of decrypting files in case of infection.
- Install antimalware tool because in most cases, it can detect ransomware in advance and remove the malware before the infection.
How to remove Digisom from your computer?
The best and easiest way to remove Digisom from your computer is to use special anti-malware program that has this threat in its database. As stated above, you need proper and reliable anti-malware program, that’s why we recommend you to use SpyHunter.
It scans your computer and detects various threats like Digisom, then completely removes it. One of the best features of this program – large threat’s database. SpyHunter’s newly advanced ransomware detection technology is able to run an instant ransomware scan and show you a message about detection. After deep scanning of your system, it will easily find and delete Digisom. Use this removal tool to get rid of Digisom for FREE.
How to decrypt .x files encrypted by Digisom?
Once you’ve removed virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Decrypt .x files manually
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.