What is Crown Ransomware?
In this article, we describe in detail Crown Ransomware. This is a threat that belongs to the number of crypto viruses. First of all, Crown Ransomware aims to encrypt user data, such as audio files, video, multimedia, archives, and so on. Of course, these files are very important for the user, which is why the question arises of how to remove Crown Ransomware and decrypt .crown files, but more on that later. Crown Ransomware encrypts user data by sending a new .crown extension. Of course, these files become unreadable and unsuitable for further use. Below we have indicated a note of the attackers, which appears in each folder with encrypted files.
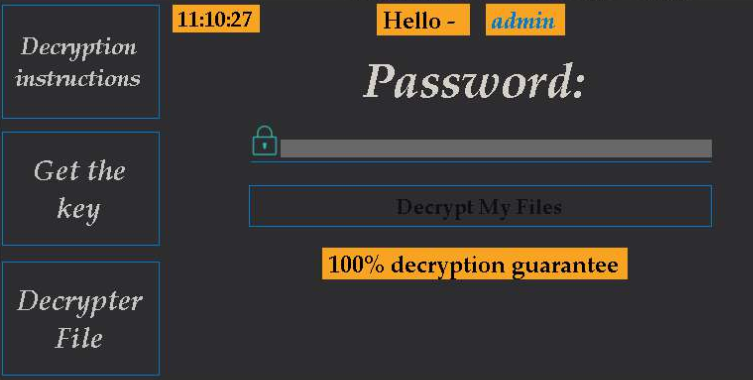
All your information (documents, databases, backups and other files) on this computer has beenencrypted using the most cryptographic algorithms. All encrypted files are formatted .CROWN. This form files .CROWN is a joint development American Hackers. You can only recover files using a decryptor and password, which, in turn, only we know. It is impossible to pick it up. Reinstalling the OS will not change anything. No system administrator in the world can solve this problem without knowing the password In no case should you modify the files! But if you want, then make a backup. Drop us an email at the address hghtllfh77137@gmail.com with your PC name You have 48 hours left. If they are not decrypted then after 48 hours they will be removed!!!
The note indicates the contacts of the attackers to communicate with them. Also, they are trying to intimidate the user, indicating the limited time to pay the ransom (48 hours). In case of non-payment, fraudsters threaten to delete all user files. Do not believe these tricks and intimidations. Ideally, use our recommendations to remove Crown Ransomware and decrypt .crown files.
Update: Use following service to identify the version and type of ransomware you were attacked by: ID Ransomware. If you want to decrypt your files, please follow our instruction below or, if you have any difficulties, please contact us: submit@securitystronghold.com. We really can help to decrypt your files.
How to remove Crown from your computer?
You may try to use anti-malware tool to remove Crown ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .Crown files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Crown ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D