CMD ransomware encryption process
CMD ransomware is a freshly made type of a very widespread Dharma ransomware. This virus usually attacks computers by the means of malicious email attachments, but there are also other ways, like direct attacks of open ports, malicious websites, bundles and etc. If the virus is successfully injected into the system, it proceeds 2 processes: scanning for media files and documents and encryption itself. After it your files are unreadable and you may notice that the extensions of them have been changed to .[Jsmith1974@mail.fr].CMD ones. Don’t try to remove this extension by yourself, as it may cause the damage beyond repair. If it was so easy to repair such files, hackers won’t get any profit of it. That’s why they left special notes that provide information on the price for decryption and contacts. In the case of infection with CMD ransomware this file is called RETURN FILES.txt and contains the following information:
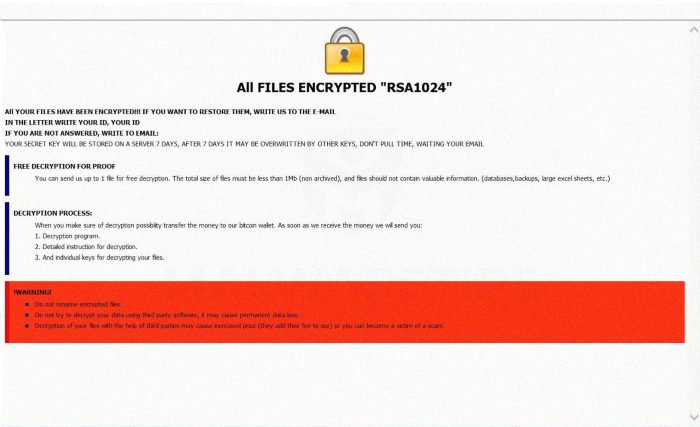
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL jsmith1974@mail.fr
IN THE LETTER WRITE YOUR ID, YOUR ID
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: jsmith1974@mail.fr
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
All your data is encrypted!
for return write to mail:
jsmith1974@mail.fr
Don’t pay ransoms a cent! Any contact with them can make the situation even worse. Moreover, they can just steal your money and left you without a tool for decryption. If you are interested in how to remove CMD ransomware and decrypt .[Jsmith1974@mail.fr].CMD files, our guide may be helpful for you!
Article’s Guide
- How to remove CMD Ransomware from your computer
- How to remove CMD Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove CMD Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove CMD from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like CMD, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt .[Jsmith1974@mail.fr].CMD files?
Once you’ve removed the virus, you are probably thinking how to decrypt .CMD files. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Restore data with automated decryption tools
Unfortunately, due to the novelty of CMD ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.


