What is Emotet?
Emotet is one of the most malicious viruses nowadays. According to the latest news, the activity of this virus has recently grown and it spreads very fast. It’s very easy to become infected with this virus due to the ways it spreads. In the most cases, hackers use email attachment to spread it. They inject the malicious code of Emotet into regular and harmless Office documents. When such a file is opened, the operating system also executes this malicious code. If Emotet successfully got into the system, it installs the other malware (Trickbot, as the rule) and sometimes it also installs the viruses of the Ryuk file-encryption ransomware family. Moreover, Emotet also infects the devices, which are connected to the same net (as for example corporate networks). By the means of Emotet hackers steal passwords and other valuable information and then use the infected device to send spam messages. So as you can see it’s very important to identify and remove Emotet virus. For this reason, we’ve prepared the detailed guide on how to do it!
How to identify Emotet?
Due to the behavior, antivirus programs can hardly identify Emotet virus. If you doubt whether your device is infected or not, you can check it by yourself. For this purpose you can use Farbar Recovery Scan Tool. After the scanning you should check the log file and search for the following indicators.
- HKEY_LOCAL_MACHINE\SYSTEM\CURRENTCONTROLSET\SERVICES\1A345B7
- HKEY_LOCAL_MACHINE\SYSTEM\CURRENTCONTROLSET\SERVICES\12C4567D
- (Gornyk) C:\Windows\SysWOW64\servicedcom.exe
- C:\WINDOWS\12345678.EXE
- C:\WINDOWS\SYSWOW64\SERVERNV.EXE
- C:\WINDOWS\SYSWOW64\NUMB3R2ANDL3373RS.EXE
- C:\WINDOWS\TEMP\1A2B.TMP
You can also use EmoCheck software. The developers of EmoCheck regularly update their program, as Emotet changes very fast. However, these programs can identify the infection, still they can do nothing with it.
How to remove Emotet?
If your corporate network or a home PC has been attacked by Emotet, you should immediately undertake measures in order to prevent aftermath. It’s quite clear, that there is no any manual solution on how to remove Emotet virus. However, you should follow the strict algorithms, otherwise Emotet will re-install itself. So here is it:
- Identify the infected machine(s).
- Disconnect the infected machines from the network.
- Download the patch for Eternal Blue, as Emotet installs Trickbot, which uses it.
- Disable Administrative Shares.
- Remove the Emotet Trojan.
- Change account credentials.
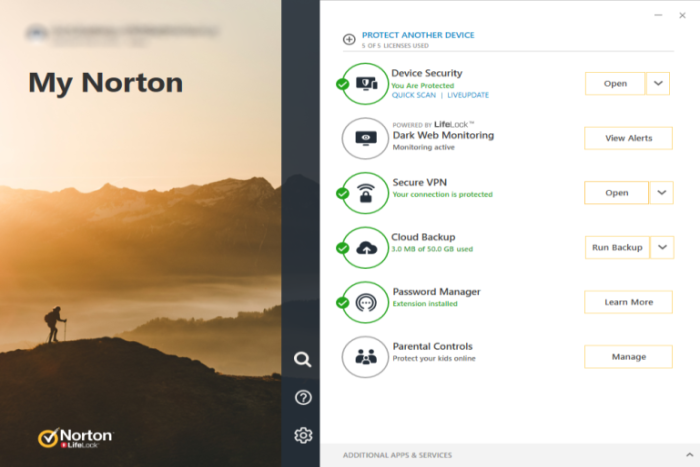
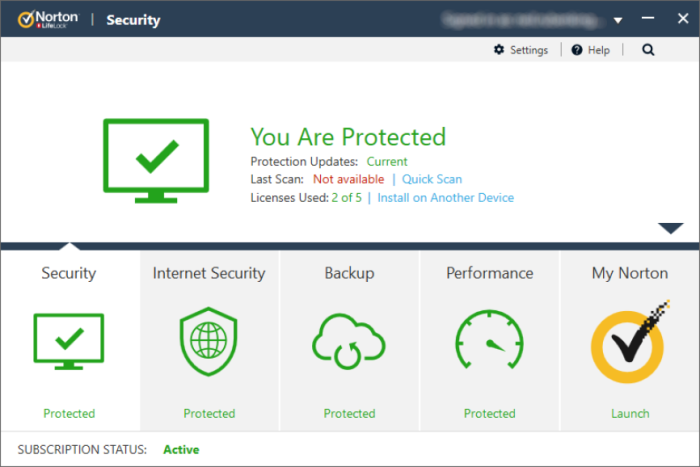
We’ve already mentioned how to detect Emotet, that’s why we won’t return to this question. The second step is necessary, as Emotet uses networks to spread and to send the information stolen from your devices. Then you should patch the Eternal Blue. Trickbot installed by the means of Emotet uses backdoors in this software in order to spread through your company’s network. Then, if the virus was removed from the infected device, it will reinstall it from the other. Then you should disable Administrative Shares as Emotet uses it to get remote access to every disk volume on your network-connected system. Then you should remove Emotet itself. For this purpose, you should use strong antivirus protection, that can detect and remove this threat from your device. Our choice is Norton 360 . Norton 360 scans your computer and detects various threats like trojans, hijackers, ransomware viruses and can definetely detect Emotet, Trickbot and viruses of the Ryuk file-encryption ransomware family. Moreover, its realtime protection can easily prevent execution of the malicious code injected into documents and other files!

CONCLUSION: so in this article we’ve mentioned all possible ways on how to detect and remove Emotet trojan from your network or personal computer. With the help of our guide you can easily detect this threat and stop its spreading. However, nowadays there is no any manual solution on how to remove it, however, Norton 360 can easily do it. It can easily prevent attacks of Emotet and Trickbot, and moreover, it can prevent attacks of numerous ransomware viruses.