What does .KODC mean?
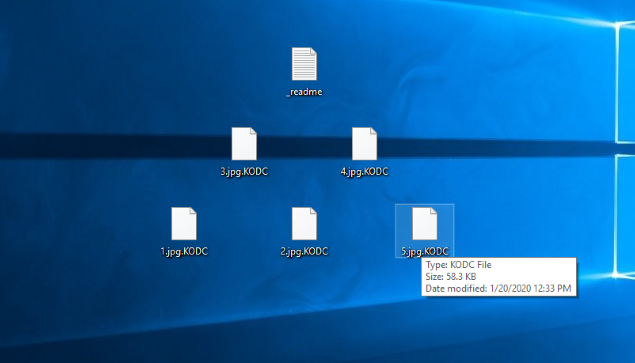
The one of the most widespread family of file-encryption ransomware viruses called STOP(DJVU) has got a new member. KODC ransomware aims at the preventing victims from the accessing to the definite file formats by the means of modifying their structures. Such files get new extension – .KODC after the encryption process. The only members of this family nowadays are TOPI, REHA, Nosu and PORET ransomwares and they have a lot in common. As the rule, KODC ransomware spreads itself by the means of fake installators. Such installators as the rule are distributed through various file sharing services and torrent trackers. However, hackers also use email attachments and remote access to spread it. For example, they usually write emails as if they come from trustful companies and try to force victims into opening a file, that contains the code of the virus. The code executes, once the file has been opened and immediately begins to make changes in the operating system. At first KODC ransomware makes changes in the Registry in order to make a system think, that it’s a legit process. Then it begins the scanning of the hard drive, as it can modify only definite files. In the most cases, such files are all formats of the documents and a great variety of the media files. The choice is not random. For the most of the victims such files are the most valuable data and they are very likely to pay for the decryption. When the process is done, the virus creates the ransom note, called _readme.txt. The purpose of this note is to assure victims, that with the one payment their files will be surely decrypted. However, in the most cases, hackers simply stop all contacts with the victims, once they’ve been paid. Regrettably, the surest way to decrypt .KODC files is to get the decryptor from the hackers, but we have solutions that can possibly help you. Read our guide on how to remove KODC ransomware and decrypt .KODC files for free!
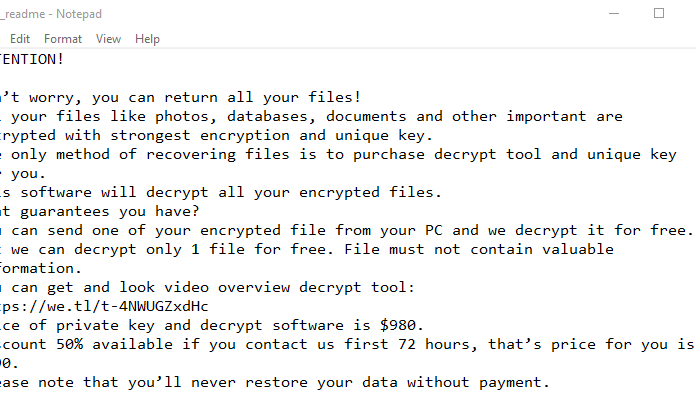
_readme.txt
Don't worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-Oc0xgfzC7q
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.
To get this software you need write on our e-mail:
helpmanager@firemail.cc
Reserve e-mail address to contact us:
helpmanager@iran.ir
Your personal ID:
*ID*
Article’s Guide
- How to remove KODC Ransomware from your computer
- How to decrypt KODC files
- Data Recovery
- Automated decryption tools
- Other software
How to remove KODC Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove KODC from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like KODC, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt .KODC files?
Once you’ve removed the virus, you are probably thinking how to decrypt .KODC files or at least restore them. Let’s take a look at possible ways of decrypting your data.
Restore .KODC files with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Decrypt .KODC files with other software
Unfortunately, due to the novelty of KODC ransomware, there are no decryptors that can surely decrypt encrypted files. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Decrypt .KODC files with Emsisoft decryptor
This software includes information about more than 100 viruses of STOP(DJVU) family and others. All that you need are two files or some luck. You can freely use it as it distributes free of charge. If it doesn’t work for you, you can use another method.
Restore .KODC files with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .KODC files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
This software includes information about more than 100 viruses of STOP(DJVU) family and others. All that you need are two files or some luck. You can freely use it as it distributes free of charge. If it doesn’t work for you, you can use another method.
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .KODC files with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Was this tutorial helpful?[Total: 0 Average: 0]
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.