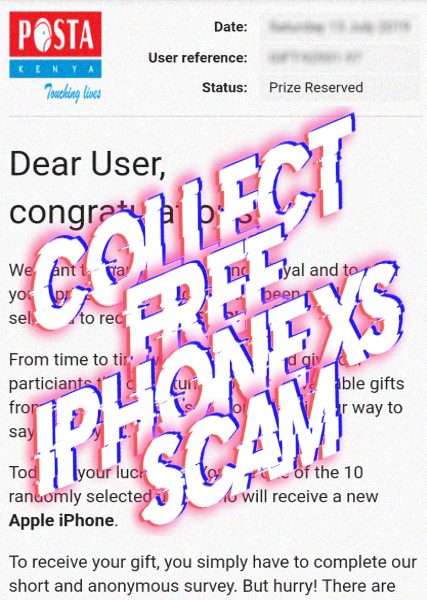
Your IP address has been randomly selected to collect FREE iPhone XS scam
Is your IP address has been really selected to collect FREE iPhone XS? Unfortunately, you’ve just faced a scam message. It has been recently reported, that a great many of the users received the message from rewards-and-prizes.alhikmahtoyan.org. Such messages as: “Your IP address has been randomly selected to collect FREE iPhone XS”, are not rare … Read more