What is Osk ransomware?
There were a lot of older versions of Scarab ransomware, and Osk ransomware is the newest. There are no significant differences between them, still the virus is very infectious and dangerous for any system. Osk ransomware can block all the personal files on your computer and makes it unreadable. First Osk infiltrates your system, then starts encrypting procedure with AES encryption algorithm. This ransomware adds .osk file extension to the name of all the encrypted data and completely changes name of encrypted files, so that they become unrecognizable, for example: 3avEeSVb4WcWOrIQVNHq5IFjxkNTXBjmi1JINs3KaFjfOVLs+=QP1qKt.osk. In this article you can learn how to remove Osk ransomware and decrypt .osk files.
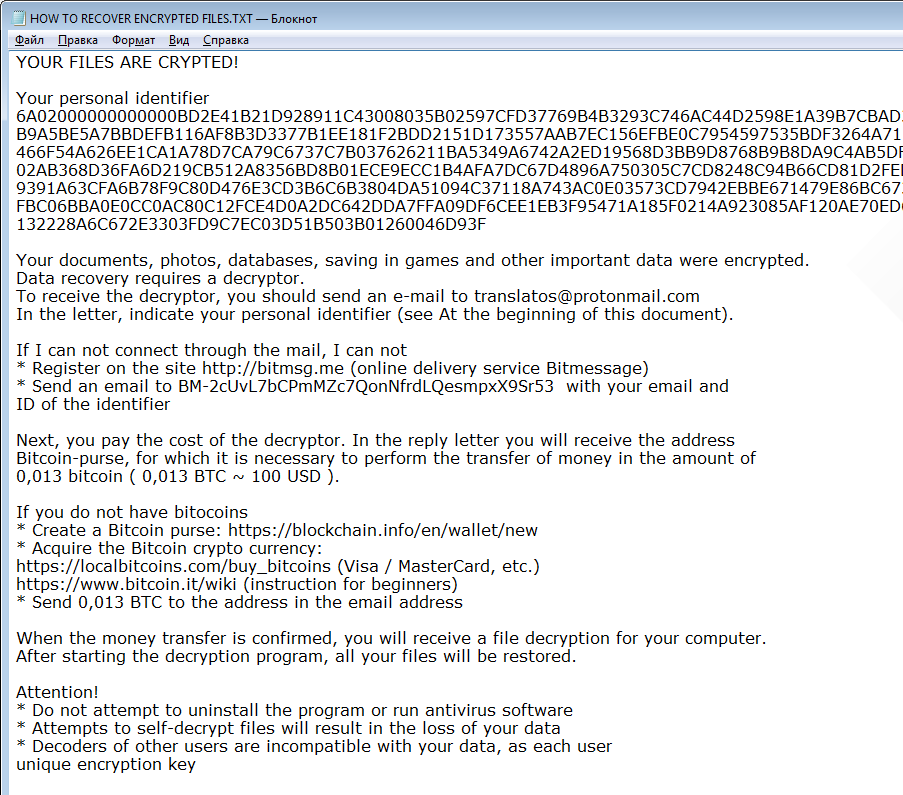
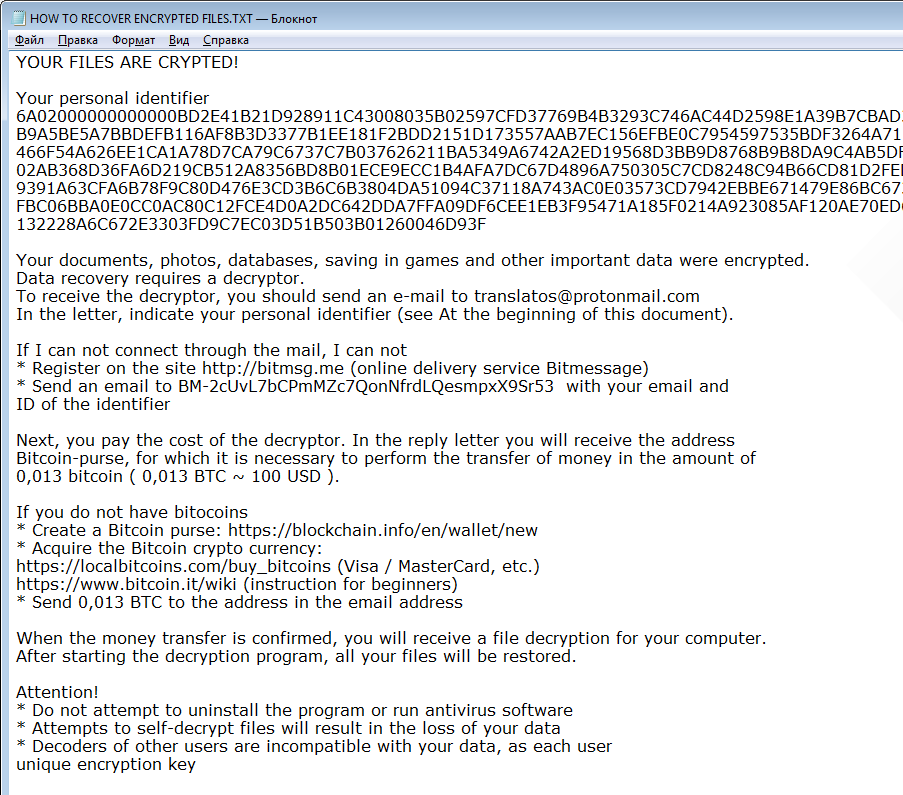
Once data on your computer is encrypted, Osk will drop HOW TO RECOVER ENCRYPTED FILES.TXT file. You can find demands and instruction on how to pay the ransom for decryption key in this text file. This is what Osk ransom note contains:
YOUR FILES ARE CRYPTED!
Your personal identifier
6A02000000000000***46D93F
Your documents, photos, databases, saving in games and other important data were encrypted.
Data recovery requires a decryptor.
To receive the decryptor, you should send an e-mail to translatos@protonmail.com
In the letter, indicate your personal identifier (see At the beginning of this document).
If I can not connect through the mail, I can not
* Register on the site http://bitmsg.me (online delivery service Bitmessage)
* Send an email to BM-2cUvL7bCPmMZc7QonNfrdLQesmpxX9Sr53 with your email and ID of the identifier
Next, you pay the cost of the decryptor. In the reply letter you will receive the address Bitcoin-purse, for which it is necessary to perform the transfer of money in the amount of 0,013 bitcoin ( 0,013 BTC ~ 100 $ ).
If you do not have bitocoins
* Create a Bitcoin purse: https://blockchain.info/en/wallet/new
* Acquire the Bitcoin crypto currency:
https://localbitcoins.com/buy_bitcoins (Visa / MasterCard, etc.)
https://www.bitcoin.it/wiki (instruction for beginners)
* Send 0,013 BTC to the address in the email address
When the money transfer is confirmed, you will receive a file decryption for your computer.
After starting the decryption program, all your files will be restored.
Attention!
* Do not attempt to uninstall the program or run antivirus software
* Attempts to self-decrypt files will result in the loss of your data
* Decoders of other users are incompatible with your data, as each user unique encryption key
Osk is a typical ransomware, its main purpose is to force you to pay them. After finishing encrypting process, the ransomware will state that there are no ways to recover your files but to pay ransom. Cyber criminals demand ransom about 100$ in BitCoins. Once you’ve done payment, they are suppose to send you decryption key. But you should know that cyber criminals are not going to give you a decryption key. Mostly they are just ignoring their victims. That’s why there is no need to contact them, it wouldn’t help. Still, Osk ransomware does very complicated encryption, but it does not damage, move or delete your files, which means you have chance to restore your personal data.
How to remove Osk ransomware from your computer and restore files?
You may try to use anti-malware tool to remove Osk ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .osk files encrypted by Osk?
Once you’ve removed virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Decrypt .osk files with automated decryption tools
Unfortunately, due to novelty of Osk ransomware, there are no available automatic decryptors for this virus yet. Still, there is no need to invest in malicious scheme by paying ransom. You are able to recover files manually.
Decrypt .osk files manually
You can try to use one of these methods in order to restore your encrypted data manually.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
How to protect PC from Osk?

It’s pretty difficult task to get rid of any ransomware, including Osk. But you can easily prevent any infection of your PC. HitmanPro.Alert’s CryptoGuard can help you with this problem. It’s one of the best anti-ransomware applications. No matter how sneaky it is, HitmanPro.Alert’s CryptoGuard will stop Osk infiltration to your system. After detection, this program removes all the related to the ransomware data and prevents your file from being encrypted.

 SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to