What is Zoh Ransomware?
Zoh Ransomware is a cryptovirus, which is a member of the Dharma Ransomware family, which more than once shone in the tops of cryptovirus articles and this is not an accident. First of all, you need to understand what exactly Zoh does. It infiltrates the user’s PC and encrypts user files of various kinds and formats. For example, it can encrypt MS Office documents, audio and video files, archives and multimedia, in a word, those files that the user does not want to lose ever, that is why the question of how to remove Zoh Ransomware is so acute.
After encryption, Zoh Ransomware assigns the simple extension .zoh or compound extension [user ID].[restdoc@protonmail.com].zoh to the attacked files, as a result of which it becomes unusable.
Here are some examples of how your files can change under the influence of Zoh Ransomware:
nature.png - nature.png.id-5483214.[restdoc@protonmail.com].zoh
report.docx - report.docx.id-5483214.[restdoc@protonmail.com].zoh
trombone.m4a - trombone.m4a.id-5483214.[restdoc@protonmail.com].zoh
Looking ahead, we note that the first part of the extension is an email address for communicating with attackers.
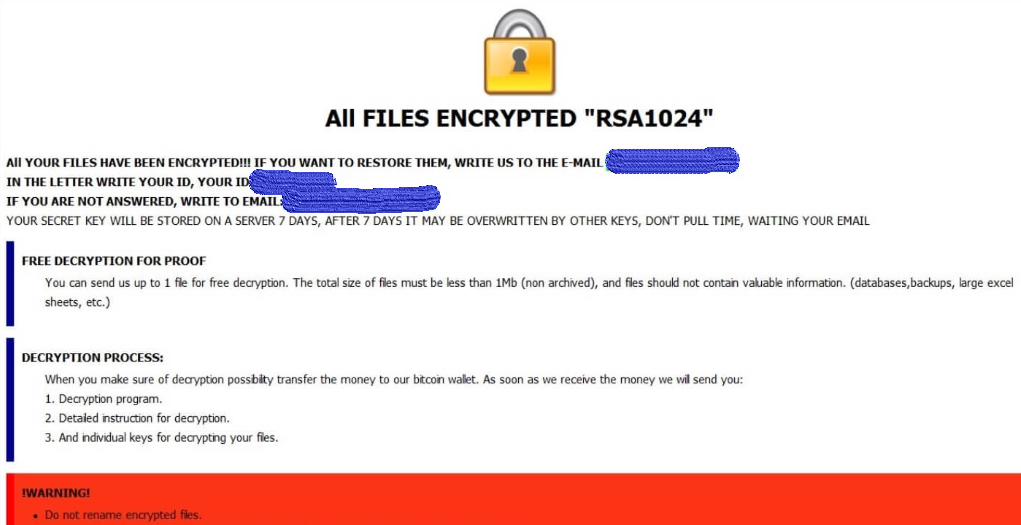
The cryptovirus creates a special text file RETURN FILES.txt that contains the detailed scammers’ requirements. Here are the note’s content and image:
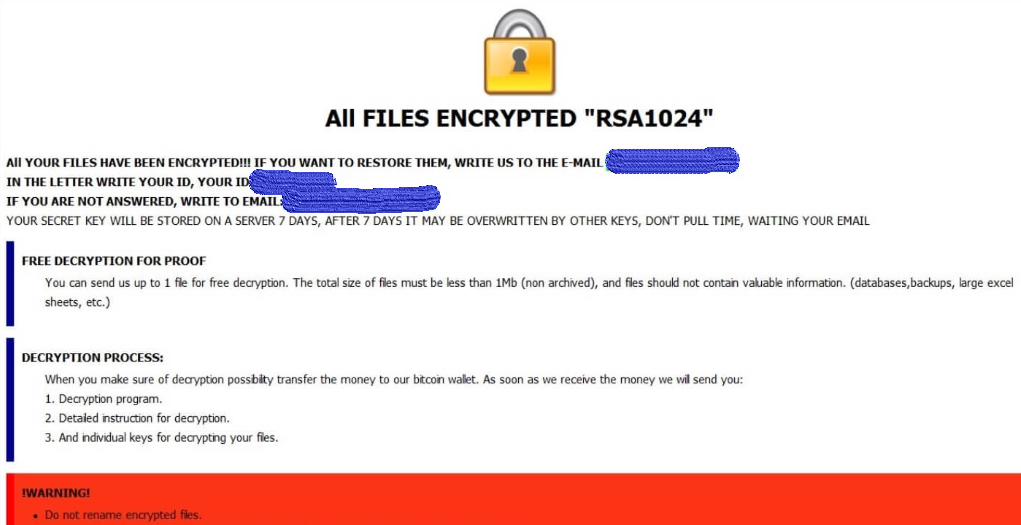
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL restdoc@protonmail.com
IN THE LETTER WRITE YOUR ID, YOUR ID
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: bigbro1@cock.li
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.All your data is encrypted!
for return write to mail:
restdoc@protonmail.com
According to the note, fraudsters need to contact them for further payment of ransom, the size of which varies. The sum starts at $500 and the maximum amount is $1,500. A lot of money, is not it? Moreover, the ransom must be paid in cryptocurrency, namely in bitcoins. This is how attackers try to hide the traces of their activities.
In addition, fraudsters resort to an effective trick, indicating in a note that the user has only 7 days to pay them a decryption fee, otherwise, the decryption key will be deleted permanently. The trick is that there is no guarantee that your files will be decrypted, even if you pay within 5 minutes, so we do not recommend you pay! Must warn that remove Zoh manually it is almost an impossible task because the virus deletes the shadow copies of files and system restore points, but below we have specified a list of tools to get rid of Zoh Ransomware automatically.
How to remove Zoh from your computer?
You may try to use anti-malware tool to remove Zoh ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .zoh files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of zoh ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D

 SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to