Viagra Ransomware encryption process
Viagra is a new type of malware which belongs to the class of ransomware viruses. It means that this malicious software is aimed at changing the structure of your files in order to make them unreadable. Before this process begins, Viagra is scanning your data and seeks for documents and media files. When it’s done, Viagra encrypts your files according to the special algorithm and changes the extension of your files to .*random 8 symbols*==ObcK (.TTyv2vQ9bDL1RvSzKi2Ns1==ObcK). Don’t try to remove Viagra ransomware encryption by yourself, you can corrupt your files at all! There is only one purpose of these attacks – hackers want to make you pay them. Usually they inform you about the decryption price by the means of ransom notes. In our case, it’s called README-VIAGRA-ObcKWm4z.HTML:
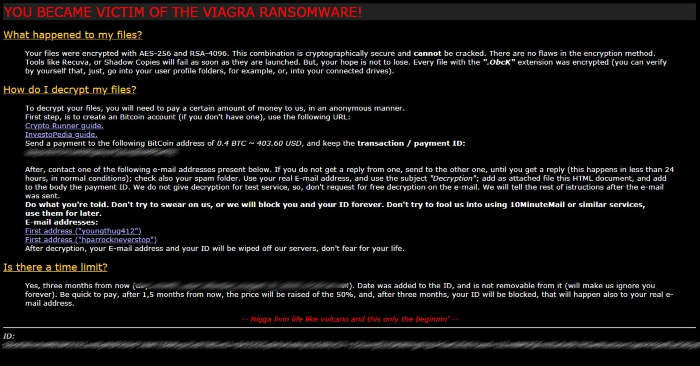
YOU BECAME VICTIM OF THE VIAGRA RANSOMWARE!
What happened to my files?
Your files were encrypted with AES-256 and RSA-4096. This combination is cryptographically secure and cannot be cracked. There are no flaws in the encryption
method. Tools like Recuva, or Shadow Copies will fail as soon as they are launched. But, your hope is not to lose. Every file with the ".ObcK" extension was encrypted
(you can verify by yourself that, just, go into your user profile folders, for example, or, into your connected drives).
How do I decrypt my files?
To decrypt your files, you will need to pay a certain amount of money to us, in an anonymous manner.
First step, is to create an Bitcoin account (if you don't have one), use the following URL:
Crypto Runner guide. https://cryptorunner.com/get-started-with-bitcoin/
InvestoPedia guide. https://www.investopedia.com/tech/how-to-buy-bitcoin/
Send a payment to the following BitCoin address of 0.4 BTC ~ 403.60 USD, and keep the transaction / payment ID:
*ID number*
After, contact one of the following e-mail addresses present below. If you do not get a reply from one, send to the other one, until you get a reply (this happens in less
than 24 hours, in normal conditions); check also your spam folder. Use your real E-mail address, and use the subject "Decryption"; add as attached file this HTML
document, and add to the body the payment ID. We do not give decryption for test service, so, don't request for free decryption on the e-mail. We will tell the rest of
istructions after the e-mail was sent.
Do what you're told. Don't try to swear on us, or we will block you and your ID forever. Don't try to fool us into using 10MinuteMail or similar services,
use them for later.
E-mail addresses:
First address ("youngthug412") youngthug412@protonmail.com
First address ("hparrockneverstop")hparrockneverstop@protonmail.com
After decryption, your E-mail address and your ID will be wiped off our servers, don't fear for your life.
Is there a time limit?
Yes, three months from now (day, month, year; *date*). Date was added to the ID, and is not removable from it (will make us ignore
you forever). Be quick to pay, after 1,5 months from now, the price will be raised of the 50%, and, after three months, your ID will be blocked, that will happen also to
your real e-mail address.
-- Nigga livin life like vulcano and this only the beginnin' --
ID: *ID number*
As you can see hackers try to put pressure on you. We strongly recommend you to not believe them, as they can trick you. They are free to take your money and left you. So you don’t have any guarantee that they will honor their promises. If you wonder, how to remove Viagra ransomware and decrypt .*random*==ObcK files, you are welcome to read our guide!
Article’s Guide
- How to remove Viagra Ransomware from your computer
- How to remove Viagra Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove Viagra Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove Viagra from your computer with all of its leftovers and register files.
Solution for Windows user: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like Viagra, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt .ObcK files?
Once you’ve removed the virus, you are probably thinking how to decrypt .ObcK files. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Viagra ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.