What is Velso?
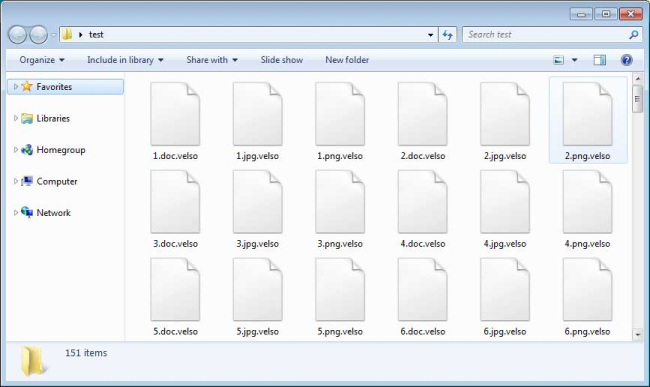
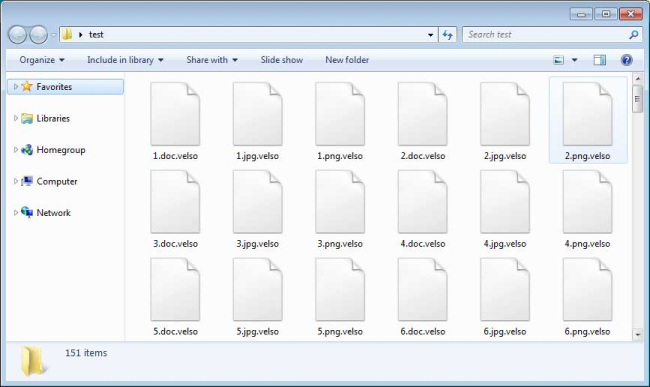
Velso is a cryptovirus that can make all your personal files unavailable. Velso is classified as a ransomware-type virus, as it demands ransom for data recovery. Within the process of virus impact, such data like photos, videos, documents will be encrypted and appended with .velso or .david extension.
Example on encrypted files:
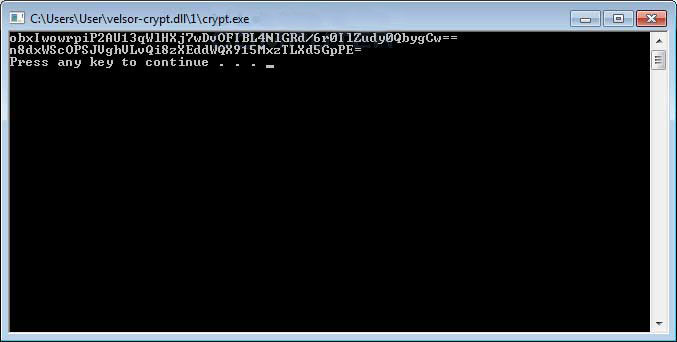
Interesting that encryption procedure is triggered manually, cybercriminals execute the malicious file via remote desktop services that causes the following window:
Once the encryption procedure is done, the user is no longer able to use affected files. Users are also provided instructions to recover encrypted files in form of TXT file (get_my_files.txt) which virus places on the desktop.
This is what Velso ransom note contains:
Hello. If you want to return files, write me to e-mail MerlinVelso@protonmail.com
Your userkey: 5A/CljSFPSSEF+M59X04Ir2HFpSAkRwNppyGkF/5jJWpCsmIBnHP8A==
The upgraded version contains following text:
*** ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED ***
To decrypt your files you need to buy the special software
You can find out the details / buy decryptor + key / ask questions by contact for communication (email):
davidfreemon2@aol.com
Here is used a typical scheme of all ransomware-type viruses – to make victims pay them. The only differences between them are the ransom price and encryption method. Cybercriminals state that there are no ways to recover your files but to pay a ransom. Once payment is done, they are supposed to send you decryption key. But you should know that nobody can guarantee that they will fulfill their end of the bargain. The practice shows that cyber-criminals just ignore people who paid them. That’s why there is no need to contact them, it wouldn’t help. Still, Velso ransomware does very complicated encryption, but it does not damage, move or delete your files, which means you have a chance to restore your personal data, but for now, you should focus on removing Velso ransomware.
How to remove Velso from your computer?
You may try to use anti-malware tool to remove Velso ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.

How to decrypt files encrypted by Velso?
Decrypt .velso and .david files manually
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Velso ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.